On 5 December 2023, the Intelligence and Security Committee (ISC)
of the U.K. Parliament published a report on the U.K.’s international intelligence partnerships.
As the report states, the “partnership with the other Five Eyes
countries is – and will remain – the most important element of the [U.K.] Intelligence
Community’s international engagement.” The U.S. is by far the largest and most
important of the Five Eyes partners, but Canada and the other countries also
get some attention in the report, and on the topic of Canada the committee
makes a couple of intriguing assertions.
More advanced capabilities
One assertion is that some of Canada’s intelligence
capabilities are “more advanced” than those of the U.K.:
“The UK–Canadian intelligence partnership is mutually
beneficial. Some of Canada’s capabilities – for instance, *** – are “more
advanced” than the UK Intelligence Community’s, and CSIS and CSE provide
valuable reporting on a range of intelligence topics.” (p. 83)
(The ISC uses three asterisks to indicate where text in the
classified version of its report has been redacted.)
Here, the committee was probably thinking mainly of CSE’s
Canadian Centre for Cyber Security:
“GCHQ noted in particular Canada’s mature and leading role
on cyber security within the Five Eyes: Canada has been with us at the head
of the pack on cyber security and our relationship on cyber security is
extremely strong and deep. It’s the deepest of the Five Eyes actually and they
have pioneered some things that we are using, including how you monitor for
threats across government, and similarly we’ve shared capability in the other
direction. So I think Canada is really nimble and they’re very focused on cyber
security.” (pp. 83-84)
Canada’s development of host-based sensors is perhaps the
best known example of Canadian cyber security technology transfer to the U.K.
But the ISC also praises Canadian intelligence collection
and/or analysis capabilities. Unsurprisingly, however, on that subject they leave
us guessing as to what exactly Canada is good at: “GCHQ also highlighted
Canada’s “very good analytical understanding ***” and the fact that, ***,
Canada has become a “world leader in ***”.” (p. 84)
The sun never sets on the UKUSA empire
Also interesting is the report’s description of a Five Eyes
practice known as “follow the sun,” a term that I hadn’t seen before.
The Chief of Defence Intelligence “explained to the
Committee that geography enables the Five Eyes to achieve more complete and
consistent intelligence coverage. This is done through so-called ‘follow the
sun’ working, whereby high priority tasks can be ‘passed’ around the Five Eyes community
to allow 24-hour working: imagery analysts that are at [RAF] Wyton … hand
the mission on to analysts that are in Washington D.C. or St Louis and to our
Canadian partners who will then hand on to Australian and New Zealand partners
who then hand back to us” (p. 65)
The Canadian partners specifically referred to here are
presumably analysts at the Canadian Forces Joint Imagery Centre, which is part
of the Canadian Forces Intelligence Command (CFINTCOM).
The report also describes a new building at RAF Wyton that
hosts not only British imagery (and other INT) analysts, but also analysts from
the other Five Eyes countries.
“[Defence Intelligence] has taken significant steps to
integrate Five Eyes partners into its work through the development of its
‘Pathfinder’ facility at RAF Wyton. This was described to the Committee as “a
unique experiment within the Five Eyes community … designed from the outset to
accommodate Five Eyes working, both in terms of having Five Eyes personnel on
the floorplate ***”.” (p. 63)
Note the flags of all five countries flying at the entrance to the building.
The Pathfinder building was described in 2014, one year
after its construction, as “headquarters to [the U.K.’s Joint Forces
Intelligence Group] and home to the Defence Intelligence Fusion Centre (DIFC).”
“Within the new Pathfinder Building at Wyton, the Joint
Intelligence Operations Centre (JIOC) coordinates Intelligence, Surveillance
and Reconnaissance (ISR) for Defence, while the DIFC brings together Geospatial
intelligence for the Nation and Intelligence Fusion for Defence.”
The image below is an architect's rendering of the building's interior.
Whether Canada has personnel in the building and, if so,
whether it is one or two analysts working on exchange or a somewhat larger
formal detachment has not been revealed.
I would assume that the SIGINT part of the Five Eyes partnership also
benefits from the use of follow the sun working, although the partner agencies focus
their efforts on national priorities and also divide some of their work
according to geographic and topical specialties.
The Five Eyes SIGINT partners also exchange
personnel and, in some cases, have deployed detachments to work at partner facilities.
In Canada’s case, CSE has a liaison office and also some
personnel serving on exchange with GCHQ, and normally at least two members of
the Canadian Forces Information Operations Group are on exchange at RAF Digby,
home of the Joint Service Signals Organization, JFIG’s SIGINT component.
With respect to the Canada-U.K. SIGINT relationship more
generally, the committee concluded that “it is apparent that GCHQ’s partnership
with its CSE counterparts – described as “flourishing” to the Committee – is
particularly strong.” (p. 83)
Canada joined UKUSA in 1948?
Another interesting claim in the committee’s report is that
Canada joined UKUSA in 1948.
“The 1946 British–US Communication Intelligence Agreement –
subsequently known as the UKUSA Agreement – formalised the SIGINT partnership
and committed the UK and US to an unprecedented level of peacetime
co-operation. The UKUSA Agreement was subsequently extended to include Canada
(in 1948) and Australia and New Zealand (in 1956), thereby creating the ‘Five
Eyes’ intelligence-sharing alliance.” (p. 61)
“Canada was the third country to join the UKUSA
intelligence-sharing Agreement (in 1948), and as such is one of the UK’s oldest
intelligence partners.” (p. 83)
Similar accounts have cropped up before.
In its 2010-11 report, the Security Intelligence Review
Committee summarized the history as follows:
“During the Second World War, Britain and the United States
worked together closely in intercepting the communications of their
enemies—what is commonly known as signals intelligence. In 1946, in the context
of the emerging Cold War with the Soviet Union, the two major powers decided to
institutionalize this cooperation through a formal agreement. Two years later,
Canada joined this alliance, with New Zealand and Australia following suit in
1956.” (p. 20)
However, in 1990, Canada’s Intelligence Advisory Committee
provided a rather different take on this history in its classified overview of
the Canadian intelligence community:
In this telling, the BRUSA (later called UKUSA) agreement
was signed in 1945; Canada, Australia, and New Zealand all agreed to join the
accord in 1946; and formal agreement incorporating all five parties was reached in 1948.
As far as I can tell, none of these accounts is quite right.
Let’s start with the IAC.
·
While the text of the BRUSA agreement had been agreed
by its U.S. and U.K. negotiators in virtually final form by November 1945, it
was formally signed by the two governments on 5 March 1946. Unless there was also an earlier signing, it’s just
wrong to say it was signed in 1945.
·
The BRUSA agreement included provision for participation
by Canada and other Commonwealth dominions in the partnership if they pledged
to abide by certain key clauses of the agreement, and Canada, Australia, and
New Zealand provisionally did so at the Commonwealth SIGINT Conference held in
February-March 1946. So, if you’re flexible about what it means to “join” the
agreement, that part of the IAC account is right.
·
In December 1947, the U.S. and U.K. moved to further
formalize the status of the Commonwealth collaborators, limiting the
anticipated pool to the existing three countries and laying out the
requirements those countries would have to follow in a new appendix to the
BRUSA agreement, Appendix J. As part of those requirements, the two parties
agreed that the U.K. would “obtain from the Sigint authorities of the
collaborating Dominions formal assurance that they will abide by the terms of
paragraphs 5, 8, and 9 of the [BRUSA] Agreement and of paragraph 5 of Appendix
E to that agreement.” In February 1948, the U.K. conveyed those assurances to
the U.S., and when the U.S. and U.K. updated the BRUSA appendices in July 1948
a footnote to that effect was added to Appendix J. These developments are
probably the basis for the claim that a formal five-party agreement was signed
in 1948. But, in fact, the BRUSA agreement remained a two-party agreement.
There is no evidence, or at least no evidence that I’m aware
of, that any actual five-party agreement that could be considered in any way
comparable to the BRUSA agreement was signed in 1948 or indeed at any time
during the Cold War. The two-party BRUSA agreement was still a two-party
agreement at the time it was renamed UKUSA in 1952, and it remained a two-party
agreement for the decades that followed. The other three countries were members
of the UKUSA partnership, were considered Second Parties, and even had some say
over portions of the agreement that affected them, but they were never
signatories, and relations among the partner agencies were mostly bilateral
rather than Five Eyes-wide.
According to an NSA document leaked by Edward
Snowden, “Although NSA has had bilateral relationships with individual Second
Party countries going back to the 1940's and 1950's, we did not have any group
(5-EYES) partnership until 1993."
It is only since the 1990s that the Five
Eyes partnership has operated on the basis of regular five-party meetings and governance
structures.
Another notable piece of negative evidence can be found in
the chronology of significant events recorded in the official History of
CBNRC (CBNRC was CSE’s name prior to 1975). The page for 1948 contains one
redacted entry and a couple of other minor redactions, but there is nothing that
might represent a major five-party SIGINT agreement. (The redacted entry is
cited to paragraph 9 of chapter 5, which discusses the competition between
strategic and tactical priorities in the naval intercept and direction-finding
program. SIGINT partners and agreements are mostly discussed in chapter 11.)
The author of the SIGINT portion of the history, former CSE
Chief Kevin O’Neill, was already a senior CBNRC official in 1948, so it is hard
to believe he would have failed to include an agreement of such importance in
this chronology if a formal quinquepartite agreement actually existed.
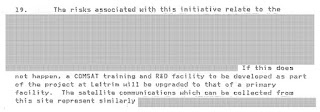
Still, for what it’s worth, a CSE document from 2013 makes
an almost identical claim, minus the five-dollar word:
So, what’s going on here?
With a vigorous amount of mental contortion, it is possible
to interpret these statements not as claims that a single, specific five-party accord
was formally agreed in 1948, but as acknowledgments that by 1948 all five
countries had in some manner formally agreed to abide by certain key BRUSA
provisions. Arguably, that was a development of some significance, although evidently
not enough to impress Kevin O’Neill.
Maybe that’s all that those statements were intended to mean. In
their plain readings, however, they just seem to be wrong.
(That said, I’d be
happy to see evidence to the contrary.)
Let’s turn now to the U.K. Intelligence and Security
Committee’s account.
The ISC, you’ll recall, reported that Canada joined UKUSA in
1948, but that Australia and New Zealand didn’t do so until 1956. Clearly, then,
the committee did not have the formal assurances that the three countries
provided to the U.K. in 1948 in mind. And the ISC certainly makes no mention of
any five-party accord in that year.
The big event that occurred in 1956 was the formal approval
by Australia and New Zealand of the conditions for SIGINT cooperation with the
U.S. that were negotiated at and in the wake of the Melbourne Tripartite Conference of September
1953 and then added to the UKUSA agreement as Annexure J1 in 1955.
At the time, Australia’s Defence Signals Branch (DSB) was a
joint British/Australian/New Zealand organization staffed mainly by Australians but with a significant British contingent and also some New Zealanders.
(New Zealand had a radio intercept program and contributed personnel to the DSB,
but it had no SIGINT agency of its own until 1977.) The 1956 developments were
the culmination of the DSB’s transition from an organization whose only
connection to U.S. SIGINT was through GCHQ to one that maintained direct
contacts and undertook joint work with the U.S. as well as the U.K.
That’s a significant milestone, and perhaps a reasonable
place to identify as the point where Australia and New Zealand truly became
UKUSA partners as opposed to just British partners.
But if that’s the criterion we use to judge Australian and
New Zealand participation in UKUSA, what does the 1948 date ascribed to Canada
correspond to?
It might be argued that the CANUSA agreement, which
formalized SIGINT relations between Canada and the United States, is the
logical counterpart to the DSB’s 1956 transition.
But the CANUSA agreement was finalized in 1949, not 1948. So,
that doesn’t explain the ISC’s date.
I can’t find anything that does explain it. Just as there is
nothing in the History of CBNRC chronology for 1948 that corresponds to
a five-party SIGINT agreement, there is nothing that suggests that the UKUSA
agreement was “extended to include Canada” during that year.
So, it’s a mystery — and one that also applies to the SIRC
account quoted above.
The idea of picking a single date may be part of the problem
here.
The integration of Canada, Australia, and New Zealand into the
UKUSA partnership is probably best understood as a gradual process of growing interaction and deepening
ties that played out over decades — a process that arguably is still playing out as the
nature of the partnership itself continues to evolve — so it is quite difficult and perhaps not very helpful to choose a specific date and proclaim it as the line between in
and out.
Even what seems like a single event can in fact extend over
several years. For example, the History of CBNRC dates Australian (and
by implication New Zealand) entry into the partnership to September 1953, the
date of the Melbourne Tripartite Conference, arguably the key decision
point in the process of integration that culminated in the 1956 formal approval of UKUSA
annexure J1 that the ISC report identifies as the moment of partnership.
In Canada’s case, if we do want to pick a year, I think neither 1948
nor 1949 is the one we ought to be looking at.
In my view, Canada was a participant in the post-war
UKUSA partnership from the start.
Canada’s residual wartime cryptologic units, consolidated
into the Joint Discrimination Unit (JDU) at the beginning of August 1945,
remained in operation when the war ended, evolving a year later into the
Communications Branch of the National Research Council (CBNRC), which ultimately
became CSE. A number of intercept stations also remained in operation, although
with reduced staffs. The Canadian government retained these facilities with the
explicit expectation that the Canadian post-war SIGINT effort would operate as
part of a greater U.S. and U.K. partnership.
Even as they were negotiating that post-war partnership, the U.S. and U.K. also anticipated that combined work with Canada would continue. By
November 1945, following consultations with Canadian officials, they had written
that expectation into the provisional text of the BRUSA agreement. Canada’s anticipated
role was also recognized in the recommendations of the Commonwealth SIGINT
Conference held in February-March 1946, which acknowledged that Canada would
not be working solely with Commonwealth partners:
"Canada's geographical position and treaty relations
with the U.S.A. make it necessary for her to be able to work directly with
Washington. The allocation of interception and cryptographic tasks and the dissemination
of Signal Intelligence results to Ottawa will therefore be matters for
consultation between Signal Intelligence authorities in Ottawa, Washington and
London."
Interim post-war assignments had already been allocated to
Ottawa by both London and Washington by that time. While Canada’s intercept and
cryptologic efforts were both very small, they were at least
marginally operational, worked directly with their U.S. and U.K. counterparts, and were in
the process of becoming more capable. In January 1947, CBNRC began working on
one of the partnership’s core efforts, processing a portion of the traffic carried
by one of the Soviet Union’s most important high-level cryptographic systems, the
teleprinter the UKUSA partners called Coleridge. The annual report of the U.S.
Army Security Agency (ASA) for fiscal year 1947 (i.e., July 1946 to June 1947) noted
that “channels of liaison with other communications-intelligence agencies were
gradually systematized and standardized by implementation of joint processing
agreements with the British (LSIC), the Navy (CSAW), and the Canadians
(CBO)."
As time went on, Canada became increasingly integrated into the partnership, exchanging liaison officers with the U.S. and securing improved access to U.S. SIGINT reporting after the
1949 CANUSA agreement, for example. The nature of Canada’s participation in the
partnership has extended and deepened in many ways in the decades since.
But
the fundamental partnership decision had been made by all three parties by the fall of 1945: although
never a signatory of the BRUSA/UKUSA agreement itself and always a junior player, Canada was a partner
from the beginning.